THE EMBEDDED AI BLIND SPOT
Blind Spot
THE OBSERVATION
Here is a reality check for your IT department.
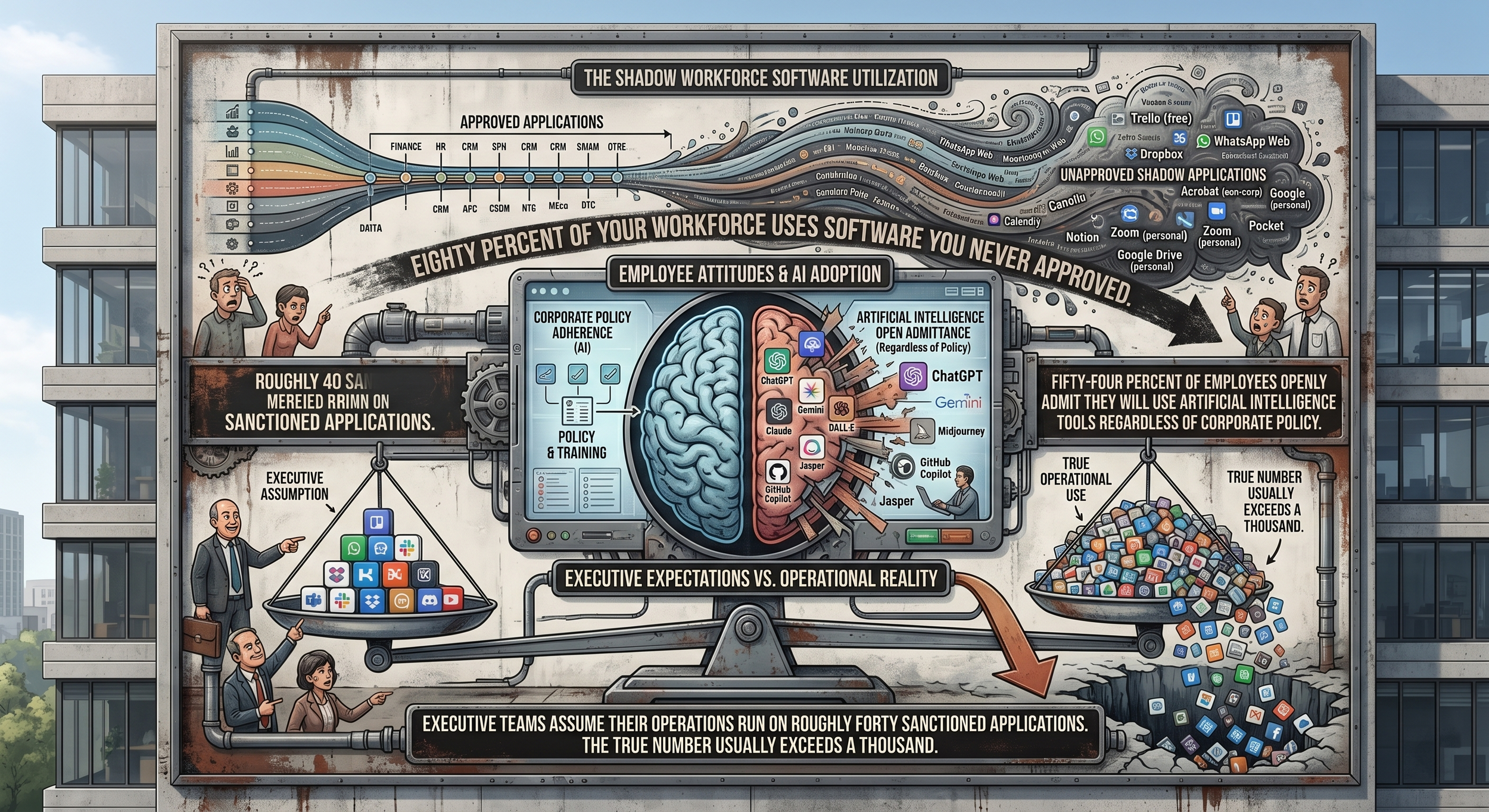
Four out of five of your employees are already using software you never cleared. Over half of them flat out admit they will use AI tools whether you like it or not. While your execs think the whole company is running on forty approved apps, the truth is closer to a thousand. You don't have a controlled tech stack. You have a massive, unmapped wild west and your policy documents are basically just wishful thinking at this point.
THE ANALYSIS
Just banning these apps is a waste of time. If you block a tool people actually like, they aren't going to stop. They are just going to hide what they're doing or find a shadier alternative that’s even harder to track. The real nightmare isn't rogue websites anymore. AI is already baked into the boring, everyday apps your team uses every single morning. It is a silent drain for your private data. Almost every major AI breach happens because someone left the back door open by ignoring basic access rules. You can't protect data that is leaking through a feature you didn't even know was turned on.
THE CHECKLIST
Stop guessing and go find the truth. Pull your logs and endpoint data to see what apps your team is actually running every day. Don't just trust a big vendor name either. Look at how each program handles your sensitive data and where it's sharing that info in public. Finally, if you have to kill a dangerous app, give your people a safe version they can use immediately. If you just take away their tools without a backup, they'll just find a shadier way to get the job done and your productivity will tank.
QUESTION FOR THE NETWORK
Are you actually hunting down every spot where AI is baked into your current tech stack, or are you just praying that basic web filters will stop the leak?
Hint: If you don't know the feature exists, you can't protect the data flowing through it. Relying on old-school filters for modern, embedded AI isn't a strategy. It's just waiting for the bill to arrive.
#ShadowIT #CyberSecurity #RiskManagement #ArtificialIntelligence #InformationSecurity
REFERENCES V2 Systems: Zero Trust for Small Businesses in 2026: A Practical Guide.
© 2026 Gnaedinger Consultancy. All rights reserved.